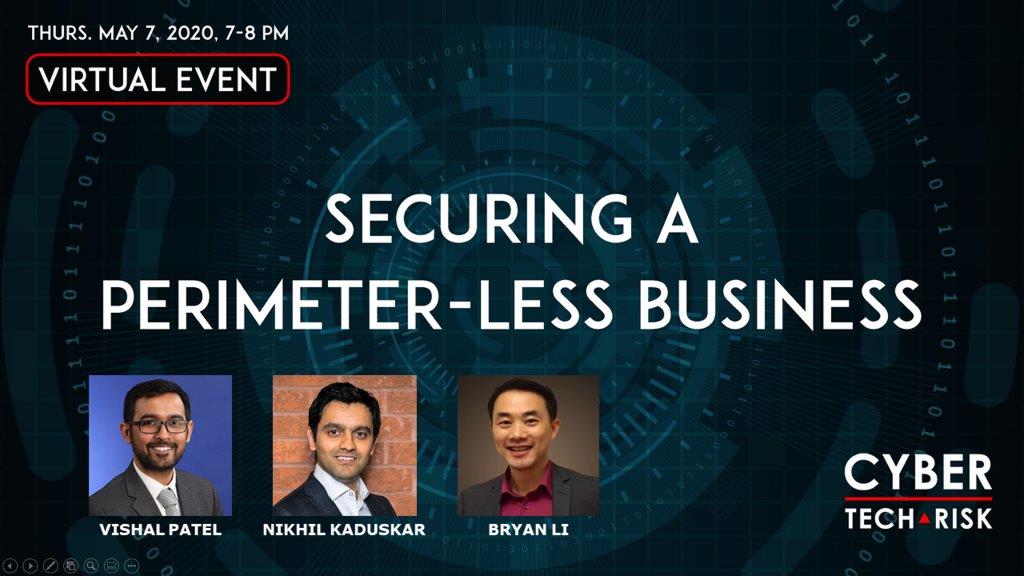
Virtual Event Highlights – Securing a Perimeter-less Business
Thursday, May 7, 2020, 7 PM – 8 PM
KEY TOPICS
1. Securing the cloud environment that hosts your assets.
2. Protecting your resources (people and technology) when there is no actual definition of enterprise network/boundaries.
3. Concepts of zero-trust architecture – how you consider each asset as untrusted and deploy strong identity and access mgmt controls to govern the environment.
Our Speakers

Vishal Patel
Cybersecurity Consultant

Nikhil Kaduskar
Cybersecurity Consultant

Bryan Li
Founder
Cyber Tech & Risk
Event Highlights

Panel Discussion Video